Какво е оценка на уязвимостите и скъпа ли е?
Alexander Sverdlov
Анализатор по сигурността

Definition
Depending on your goals, a cyber security vulnerability assessment identifies, analyzes, and prioritizes security vulnerabilities in your IT systems, networks, and applications. We might even add processes to that list. A vulnerability assessment helps you detect potential entry points that attackers could exploit and provides a roadmap for remediation.
Unlike penetration testing (pen testing, pentesting), which actively attempts to exploit vulnerabilities, a vulnerability assessment focuses on discovering and reporting them without performing real attacks.
Why is a vulnerability assessment important?
New vulnerabilities emerge daily. Your team uses all kinds of apps on their computers, the IT team installs all kinds of servers and services all the time, they set up new cloud services and your web design team makes changes to your website, while your SaaS apps gain new features (and bugs) every day. This software chaos generates vulnerabilities both in code and in configuration, all the time. A vulnerability assessment helps you to:
- Identify security gaps before hackers do.
- Reduce the risk of data breaches, ransomware, and unauthorized access.
- Ensure compliance with regulations (GDPR, PCI-DSS, HIPAA, etc.).
- Protect customer and company data from exploitation.
- Improve overall cybersecurity posture through proactive security management.
On top of that, a cyber security vulnerability assessment might be necessary for compliance with industry and government regulations. And if you really care about the safety of your data and your client's data as well, such an assessment might be important for you just in principle.
How often should a company conduct a vulnerability assessment?
I would say it should be continuous, but not every company is ready for that. Also, you can't just run a scan against your entire IT infrastructure - often times, that would make no sense.
You should prioritize the work based on risk factors such as software age, exposure to the Internet, data stored on the asset, etc.
The frequency of vulnerability assessments depends on various factors, such as:
- Industry and compliance requirements – PCI-DSS requires quarterly scans, while other regulations may have different mandates.
- Company size and risk level – Large enterprises or high-risk industries (finance, healthcare) should perform monthly or even weekly scans.
- Changes in infrastructure – Conduct an assessment after major software updates, system changes, or cloud migrations.
- Threat landscape – If there is a surge in cyberattacks, it's wise to increase assessment frequency.
Best practice: Perform at least a quarterly vulnerability assessment, with continuous monitoring for critical systems. After each assessment, work hard to automate patching and fix any wrong configuration or lousy security practices.
What are the steps involved in a vulnerability assessment?
A vulnerability assessment follows a structured process:
- Logistics - meeting with the team who is about to help you with the assessment, deciding on participants, timing, etc.
- Asset Identification – Determine which systems, applications, and devices need assessment.
- Scanning – Use automated tools (Nessus, OpenVAS, Qualys) to scan for known vulnerabilities.
- Analysis & Prioritization – Categorize vulnerabilities based on risk level (CVSS scores, exploitability, business impact).
- Remediation Planning – Develop a strategy to patch or mitigate high-risk vulnerabilities.
- Reporting – Provide a detailed report with findings, recommendations, and mitigation steps.
- Follow-up – Verify that vulnerabilities have been properly addressed in a retest.
What are the common tools used for vulnerability assessments?
Some of the most widely used vulnerability assessment tools include:
- Nessus – One of the most popular vulnerability scanners, used for network and system
- assessments.
- OpenVAS – Open-source vulnerability scanning tool with regular updates.
- QualysGuard – Cloud-based scanning for web applications, networks, and endpoints.
- Rapid7 Nexpose – Enterprise-grade scanner that integrates with Metasploit for penetration testing.
- Burp Suite – Focused on web application security testing.
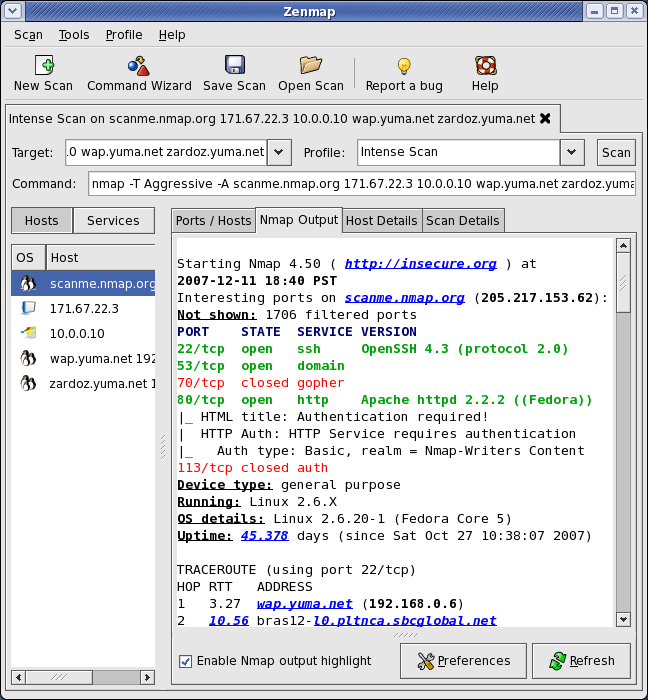
- Nmap – Network scanning tool that identifies open ports and potential vulnerabilities.
- ZAP - often used to test Web and APIs for common vulnerabilities.
Each tool has its strengths, so organizations often use a combination for comprehensive assessments. But let's not forget about the fact that we should also assess the vulnerabilities in your cloud environments - Amazon AWS, Microsoft 365 (Azure) and Google GCP. There are numerous tools to perform cloud security vulnerability assessments, most of which are published on Github and are open source. We like to perform our cloud security assessments manually, as that is the only way to discuss your setup with your team as we run the assessment.
What is the difference between a vulnerability assessment and a penetration test?
| Vulnerability Assessment | Penetration Testing |
|---|---|
| Identifies security weaknesses | Actively exploits vulnerabilities |
| Uses automated scanning tools | Uses manual techniques & tools |
| Broad, covers multiple systems | Targeted, focuses on high-risk areas |
| Low risk, does not impact operations | Higher risk, may disrupt services |
| Performed regularly (quarterly/monthly) | Conducted less frequently (annually or after major changes) |
When to choose?
- Vulnerability assessment – For routine security checks and compliance.
- Penetration testing – When you need to simulate real-world attacks to test security defenses. You should only run penetration tests after you have spent at least a year securing your systems, pipelines, code, etc. The objective of the pentest is to find omissions in your security, not being your first action in your security journey, but the last.
Can a vulnerability assessment disrupt business operations?
In most cases, a vulnerability assessment does not disrupt business operations because:
- It primarily involves scanning, which is non-intrusive.
- Most assessments are scheduled during off-peak hours to minimize impact.
- Good security tools are designed to avoid overloading systems.
However, misconfigured scans (e.g., aggressive scanning on production servers) can cause performance slowdowns or crashes. To avoid this:
- Test on non-production environments first.
- Use credentialed scans to avoid triggering false alarms.
- Monitor systems during the assessment.
Who should perform a vulnerability assessment?
A vulnerability assessment can be performed by:
- Internal IT/security teams – If they have the necessary skills and tools.
- External cybersecurity firms – Third-party experts bring experience and unbiased reporting.
- Automated scanning services – Some managed security providers offer continuous vulnerability management.
Best approach: A mix of internal and external assessments ensures thorough coverage and compliance.
What happens after a vulnerability assessment?
Once the assessment is complete, the next steps include:
- Analyze the report – Identify high-risk vulnerabilities that need immediate attention.
- Prioritize fixes – Address critical vulnerabilities first (CVSS 9.0+).
- Apply patches – Update software, firmware, and configurations.
- Implement compensating controls – If a patch isn't available, use firewalls, network segmentation, or endpoint protection.
- Retest – Conduct a follow-up assessment to ensure vulnerabilities have been fixed.
- Document & Report – Keep records for compliance audits and internal security tracking.
What are the legal and compliance requirements for vulnerability assessments?
Many regulations and industry standards require regular vulnerability assessments:
- PCI-DSS – Requires quarterly vulnerability scans for organizations handling credit card data.
- GDPR – Mandates regular security assessments to protect personal data.
- HIPAA – Healthcare organizations must identify vulnerabilities that could impact patient data security.
- ISO 27001 – Requires a risk management approach that includes vulnerability assessments.
- NIST Cybersecurity Framework – Recommends continuous monitoring and vulnerability management.
Failing to conduct assessments can result in fines, lawsuits, or data breaches.
Вижте също: The Growing Threat of Ransomware: How to Protect Your Business

Александър Свердлов
Основател на Atlant Security. Автор на 2 книги за информационна сигурност, лектор по киберсигурност на най-големите конференции по киберсигурност в Азия и панелист на конференция на ООН. Бивш член на екипа за консултации по сигурността на Microsoft, външен консултант по киберсигурност в Емиратската корпорация за ядрена енергия.