Стажове по киберсигурност: как да получите 10 оферти за 3 месеца, стъпка по стъпка!
Alexander Sverdlov
Анализатор по сигурността

Before I start this article:
Кой съм аз и защо по дяволите трябва да ме слушате?
My name is Alexander (here's my LinkedIn), and I've worked at Hewlett-Packard, Microsoft and have consulted a nuclear power plant on cybersecurity. I wrote two books on cybersecurity and have been a speaker 5 times in a row at some of the world's largest cybersecurity conferences. I run my own cybersecurity consultancy now - and if you want to learn from me, book a call using the contact form on this website - I'll charge you $400/hour but those will be the best invested money in your life!
Alternatively, you can buy my guide on getting cybersecurity internships here, and follow it on your own. Your life, your choices!
P.S. Atlant Security does not offer internships at this point (unless you are a killer content creator!). I recommend you start your career at a larger company, where you can learn from a large team.
So without further delay...
Landing your first cybersecurity internship or entry-level role is exciting-but intimidating. With cybersecurity becoming a priority for every business, competition has increased significantly. So, how can you stand out?
Whether you're transitioning from another career or fresh from training, here's exactly what you need to do.
In just three months of relentless, hard work, you can get 10 offers from the employers of your choice. This will guarantee you an amazing, interesting career that can pay you upwards of $200,000 USD per year in just 10 years or less.
Just follow my guide!
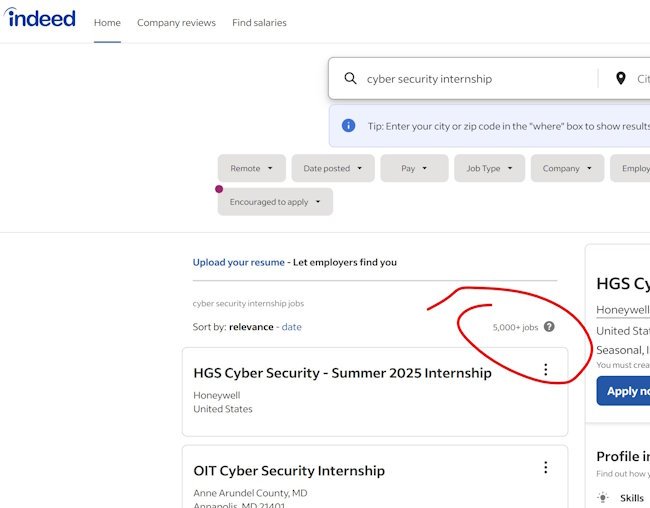
There are thousands of cybersecurity internships and entry-level jobs listed at Indeed .
And every day, each of them gets 200-500 resumes. Imagine if you were a girl, getting messages on Instagram from 500 guys every single day. How would you decide which one to ... 'hire'?
It's the same with jobs and internships. You can't get noticed by going the same route as everyone else. So my guide goes around the regular application process... but we'll talk about that later. For now, let us get the basics right.
Step 1: Clearly Define Your Goals
What area of cybersecurity interests you?
Before sending applications, clarify a few things. What do you have in the bag, that would get the eyes of a potential recruiter/employer glowing?
Which technical skills might work in your favor, perhaps you can create content, or are really good at spotting small faults in huge piles of data?
Then, define your goals:
-
Penetration Testing - if you're good at coding or like tinkering with stuff until it breaks, this is for you. Keep in mind: you do have to have programming skills to become a great penetration tester. And even in penetration testing, there are sub-fields, some of which don't require programming, such as physical penetration testing:
- Physical penetration testing
- API penetration testing
- Web penetration testing
- Application penetration testing
- Cloud penetration testing
- etc.
-
Security Operations (SOC): SOC positions are probably the easiest to get into and they can be a great stepping stone, if you play your cards right. But beware: some of the larger companies out there have a policy of a minimum tenure at one position. For example, Microsoft does not allow you to switch positions in less than a year, officially, and prefers you stay at one position for at least two years... on the interview, always ask, if you will be promoted quickly if they notice you have more to offer than the position you were initially hired for.
-
Security Audits: if you like digging into details, love Word & Excel and like interviewing people, this is the job for you!
-
Security Compliance: similar to auditing, but more closely related to legal paperwork. One of eight people just can't get their hands off documentation and paperwork. If you are one of them, go for it!
-
Cloud Security: if you are a fresh graduate and are well versed in cloud technologies (or have passed cloud courses) - upgrading to cloud security might be a logical next step.
-
Incident Response
- Forensics - cloud forensics, log forensics, disk forensics, computer forensics, etc.
- Security Leadership
Action:
Write down your ideal cybersecurity role:
-
What areas of cybersecurity excite you?
-
Are you technical (pentesting, incident response) or prefer compliance and auditing?
Step 2: Building Relevant Skills (Quickly!)
Cybersecurity isn't just theory - it's hands-on. Companies prefer people who can demonstrate real-world skills. And if they offer cybersecurity internships, these will be given to the candidates who demonstrate the most actions taken towards being applicable for the job.
Quick ways to gain practical skills:
| Skills | Resources & Links | Approx. Duration |
|---|---|---|
| Ethical Hacking | TryHackMe, Hack The Box | 2-3 months |
| Networking Basics | Cisco Networking Academy, Udemy Networking Courses | 1 month |
| Cloud Security Basics | AWS Free Tier, Microsoft Azure Free tier | 1-2 months |
| Compliance Knowledge (GDPR, ISO 27001) | EU GDPR Resources, ISO 27001 Intro courses on Udemy | 2-3 weeks |
“Employers don't just look at degrees - they look for what you can practically do for their organization.” – Lisa Ventura, Cybersecurity Expert
Step 3: Get Certified (Smartly)
You don't need 10 certifications - but one or two key certifications can open doors fast.
Top Entry-Level Certifications:
| Certification | Difficulty | Cost ($) |
| CompTIA Security+ | Beginner-Friendly | $250–$350 |
| CompTIA Network+ | Beginner-Friendly | $250–$350 |
| eJPT (Junior Penetration Tester) | Practical, Hands-On | ~$200 |
Quick Tip: Security+ is a universally recognized certification and can often get you interviews quickly.
Step 4: Craft a Cybersecurity-Focused Resume (That Actually Gets Interviews)
Most resumes fail for one reason - they’re generic. Recruiters take less than 30 seconds reviewing your resume, so be clear and concise.
DO:
-
Highlight practical experience (CTFs, HackTheBox, personal labs).
-
Showcase relevant skills (OSINT, Active Directory Security, networking).
-
Use cybersecurity keywords (SIEM, penetration testing, compliance).
DON'T:
-
List unrelated experience (unless directly applicable).
-
Overload with theory or generic soft skills.
Here’s an ideal resume section:
| Experience | Skills Demonstrated |
| Completed 50+ labs on Hack The Box (Pentesting) | Hands-on ethical hacking, vulnerability analysis |
| Home Lab: Active Directory Setup & Exploitation | Privilege escalation, Kerberos exploitation |
Step 5: Build an Online Presence (LinkedIn, GitHub)
Employers Google you first. Make it count.
-
LinkedIn: Optimize your profile clearly.
-
Professional profile photo
-
Clear headline: “Cybersecurity Analyst | OSINT Enthusiast | Active Directory Security”
-
Share regular updates: cybersecurity insights, practical tips, or stories from your learning journey.
-
-
GitHub: Host scripts, write-ups from CTFs, scripts, and tools you've developed. It signals you're genuinely passionate.
- Other social media: try to post as much as possible about cybersecurity. If you're after cybersecurity internships, you must show your active interest in the field!
Example GitHub Profile:
-
Active Directory security auditing scripts
-
Tools for automated enumeration
-
Documentation of personal projects
Step 6: Gain Practical Experience (Without a Job)
No experience? No problem. Gain practical experience by:
-
Joining CTFs: Platforms like TryHackMe and Hack The Box help you build genuine skills and confidence.
-
Volunteering: Offer to audit security for non-profits or small businesses.
-
Freelance Marketplaces: Offer entry-level assessments on Upwork or Freelancer.com.
“Practical experience - even unpaid-puts you miles ahead of competitors with certifications but no real-world application.”
Step 7: Transitioning from a Completely Unrelated Career
Switching careers into cybersecurity might feel daunting, especially if your background isn't technical. But remember: cybersecurity thrives on diverse experiences. Here's how to leverage your previous career effectively:
Identify Transferable Skills
List skills from your previous roles that are valuable in cybersecurity:
-
Problem-solving
-
Analytical thinking
-
Attention to detail
-
Communication and reporting
-
Project management
Example: If you were in finance, your analytical skills in risk assessment directly apply to cybersecurity audits and compliance.
Clearly Communicate Your Story
When talking to employers, craft a concise story that highlights why you chose cybersecurity:
“As an accountant, I constantly worked on compliance and risk management, which naturally drew me towards cybersecurity. Now, I'm building hands-on skills to apply my analytical abilities to protect sensitive data.”
But before you even speak to an employer, you must know why you chose this particular company. You will be asked this question! Research their past, their present, and their plans for the future. Read reviews from past employees, read their blog. The secret sauce would be, finding their executives and reading their posts online! If you can find your hiring manager's social media profile and follow them, you will learn a ton of information to use during your interview, strategically.
Step 8: Overcoming Impostor Syndrome
Feeling like an impostor is common. Here's how to overcome it:
-
Remember everyone starts somewhere: Every cybersecurity expert was once a beginner.
-
Track your progress visibly: Keep logs of completed courses, labs, certifications, and practical projects.
-
Engage in communities: Join online forums (Reddit, LinkedIn groups, Discord channels) to see you're not alone.
Step 9: Mastering Interviews Without Direct Cybersecurity Experience
Here's how to handle tough questions when you don’t have extensive cybersecurity experience:
Common Tough Interview Questions and Ideal Answers
| Question | Strong Answer |
|---|---|
| “Why cybersecurity after a career in marketing?” | "Marketing taught me how to analyze audience behavior meticulously. Cybersecurity requires similar attention to patterns and behaviors, making it a natural next step." |
| “Describe a cybersecurity incident you've managed.” | "Though I haven't handled a corporate incident, I've simulated incidents in labs, like detecting Active Directory compromise or phishing attacks." |
Always shift the conversation to what you've learned, your eagerness, and practical knowledge from personal labs or online simulations.
Step 10: Dealing With Rejections
Rejection is part of the process. Use it constructively:
-
Always ask for feedback: Politely ask interviewers or recruiters what you could improve.
-
Track patterns: If multiple rejections highlight the same gap, focus immediately on addressing it.
-
Stay resilient: Rejection often isn’t about capability but timing or fit.
Step 11: Advanced Strategies to Stand Out
Personal Cybersecurity Project
Initiate a cybersecurity research project or build a tool solving real problems, like a:
-
Security scanning script
-
Automated compliance checklist
-
OSINT gathering tool
Share this on GitHub and LinkedIn to demonstrate proactive learning and practical knowledge.
Create Content to Showcase Your Expertise
Publish simple yet insightful cybersecurity articles, videos, or tutorials. Potential topics:
-
How to Secure Active Directory (Beginner Guide)
-
Quick Guide to GDPR for Small Businesses
-
Simple Guide to Cloud Security
STEP 12: READ BOOKS!
When I was just starting my career in cybersecurity, I read a TON of books. I ordered so many books on cybersecurity, Amazon had to ship them to my country (Bulgaria!) in HUGE BAGS - as they did not have such large boxes!
I'll list some books here, but the full list of books I recommend will be given to my paid mentees or be in my full guide, which you can buy here.
https://www.amazon.com/Stealing-Network-Complete-Collectors-Chapter/dp/159749299X?crid=XHTJATG6WP4B&dib=eyJ2IjoiMSJ9.ZUgSDI-cw3YgSoZ5jtxiv3PT__gdvCx23L8Asi9vjM7XYFjBqfaSoGKmvEGY4zxOq5jn9IyKUaz2cvyWInr4Kxe5akjegkvp-xd_H3svGZ0I2yvV1X-umPIHYUsVY6lyZI4vMT-P-NfCYTJtuHlrvWDIGry1GV11iXnzbUcucU8iakjnrnWwCVO5DgUlZJx5gQhIEuy7lplIjIOIBAX_b7_kWflfEZfB01XkgndTK3c.tue7mO4I66LlTNha5ZSkHaIYP_rbFGF_6WPtIp_q_u0&dib_tag=se&keywords=Stealing+the+Network+series&qid=1742053894&sprefix=stealing+the+network+serie%2Caps%2C189&sr=8-1
https://www.amazon.com/dp/1593271441?_encoding=UTF8&pd_rd_w=xlUFu&content-id=amzn1.sym.7d2923e8-7496-46a5-862d-8ef28e908025&pf_rd_p=7d2923e8-7496-46a5-862d-8ef28e908025&pf_rd_r=ESS9P2NKAZ8DNK5WC469&pd_rd_wg=F7jVF&pd_rd_r=125c1149-3d1e-431e-9922-2d8f32952fa2
Read at least these two books (my guide will list dozens more, per your preference - pentesting, auditing, forensics, etc). If you are in a rush, read the Stealing the network series!!!
Step 13: DO NOT SEND RESUMES
You read that right. DO NOT send resumes.
You're applying for an internship. So do tens of thousands of people. All sending their useless pieces of paper.
I was hired at Microsoft, without a resume!
Yes, it's possible. And in your situation, if you're just starting out your career, you MUST be creative.
Pick 10 companies. Make the conscious choice of relentlessly pursuing an internship offer from all of them. Even if you get just 3 offers, you will ONLY get them if you made the choice to get an offer from all ten!
Then... read my guide or get a consultation with me. I'll give you the secret sauce on how to approach the hiring managers so that they would lose their sleep over hiring you.
Step 14: Getting the Most From Your Internship
Once you land the internship, maximize its value:
-
Document your work: Track every task, project, and skill acquired.
-
Network internally: Regularly connect with mentors and senior professionals for guidance.
-
Be proactive: Volunteer for challenging projects or additional responsibilities.
Switching careers into cybersecurity isn’t easy - but it’s achievable. With strategic planning, practical learning, consistent networking, and resilience, you can successfully transition and thrive in cybersecurity.
Need more personalized guidance? Feel free to connect - I’m here to help you launch your cybersecurity career.
Вижте също: External Network Monitoring Services

Александър Свердлов
Основател на Atlant Security. Автор на 2 книги за информационна сигурност, лектор по киберсигурност на най-големите конференции по киберсигурност в Азия и панелист на конференция на ООН. Бивш член на екипа за консултации по сигурността на Microsoft, външен консултант по киберсигурност в Емиратската корпорация за ядрена енергия.